Over $3.1 trillion in illicit money flowed through the global financial system in 2023, nearly equivalent to the market cap of Amazon and Meta combined, quite close to the nominal GDP of India (USD 3.5 trillion). Such staggering sums severely threaten the integrity and stability of our global financial system.
Financial crime doesn’t discriminate. However, fintech companies face an exceptionally high risk of being exploited. Their innovative services, which provide quick access to credit and streamlined account opening processes, can inadvertently create vulnerabilities in the system.
Regulators have developed a comprehensive set of laws called Anti-Money Laundering (AML) to combat this threat. Continue reading to understand how AML approaches money laundering and helps to maintain the trust and stability that underpin the global economy.
Understanding Money Laundering
To understand the ins and outs of AML, we first need to understand what money laundering is and how it works.
Money laundering is the process of disguising the source of illegally gained money (such as terrorist funding or drug trafficking) so it appears to have come from a legal source. It can have far-reaching economic, social, and security-related consequences globally.
The process essentially ‘launders’ this ‘dirty’ money ‘clean’, so it can be injected into the legal financial system.
Stages of money laundering
Money laundering typically occurs in three stages:
1. Placement
It involves introducing illicit funds into the legitimate financial system. Some standard methods of placement are:
- Smurfing (making multiple deposits below the AML reporting threshold)
- Commingling (blending dirty money with legit business revenues)
- Making payments to cash-based businesses like casinos to disguise the origin
- Paying off legitimate debt
2. Layering
Now these funds undergo a series of complex transactions so they’re buried within the financial system to disguise the owners’ identity. This process is called layering and it creates a convoluted audit trail.
For example, the funds may be wired from a US account to a shell company in the Cayman Islands, converted to bonds, sold, and transferred to a Swiss bank account within a short timeframe.
3. Integration
This involves reintroducing the now laundered money into the legit economy. The money is withdrawn and integrated into the economy. This is often done through:
- Real estate investments
- Acquiring luxury assets
- Securities trading
The global financial system has developed a coordinated approach in response to this growing threat — anti-money laundering.
Anti-Money Laundering Explained
Anti-money laundering is a comprehensive framework of policies, laws, and regulations designed to detect, prevent, and report money laundering. It addresses a wide variety of crimes, such as corruption, market manipulation, tax fraud, terrorism financing, and drug/human trafficking.
Anti-money laundering acts are created by global and local regulators and applied to financial institutions (FIs) and other regulated entities, such as:
- Banks and credit unions
- Insurance companies
- Asset reconstruction companies
- Gaming businesses and casinos
Different countries have different acts that FIs must adhere to.
India’s Key AML Acts
Prevention of Money Laundering Act (PMLA) is a critical anti-money laundering act in India, enacted in 2002 and subsequently amended multiple times, the latest being in 2023.
PMLA is enforced by the Enforcement Directorate (ED) under the Ministry of Finance. It works with the Financial Intelligence Unit-India (FIU-IND) to combat money laundering and terrorist financing, with the latter providing financial intelligence to the former.
India is also a member of the Financial Action Task Force (FATF) — a global organization with the aim “to develop policies to combat money laundering and to maintain certain interests.” It sets standards and promotes effective implementation of the AML. At the time of its formation, it had 16 members, though the number was 40 in 2023.
The Foreign Exchange Management Act (FEMA) was enacted to prevent money laundering through cross-border transactions. While its primary purpose is to regulate forex transactions, it limits the amount of foreign currency that can be taken out of or brought into India. Plus, it gives authorities the power to examine and investigate suspicious foreign exchange transactions.
A Brief History of PMLA
A brief history of India’s PMLA is shown in the following image:
The Importance of AML for FIs
In the wake of the 2008 financial crisis and the rise of financial crimes, regulators have tightened oversight on traditional FIs and fintechs. The fintech sector, in particular, faces increased scrutiny due to its rapid growth and innovative business models.
For instance, India’s fintech market alone is projected to reach $1.5 trillion by 2025. While this growth is driven by cutting-edge technologies, it also introduces new vulnerabilities that criminals may exploit. AML compliance is, therefore, substantial in:
- Combating financial crime: The UN Office on Drugs and Crime estimates that 2–5% of global GDP or $800 billion–$2 trillion is laundered annually. AML measures help detect various forms of financial crimes.
- Maintaining the integrity of the system: AML restricts bad actors’ access to financial resources, thus contributing to the overall stability and trustworthiness of the global financial system.
- Risk Management: Effective AML programs help institutions identify and mitigate risks associated with their products, services, and customer base.
Consequences of Non-Compliance for FIs
The stakes are high — over $485 billion were lost to fraud scams and bank fraud schemes in 2023 despite the current AML measures. Unsurprisingly, if the FIs and fintech don’t comply with the AML, regulators can impose sanctions and disciplinary actions:
AML Compliance Framework
To comply with the Anti-money Laundering Act, FIs need to register as reporting entities with FIU-IND and follow a set of requirements that form the foundation of an effective AML program:
- Create internal policies to detect and prevent laundering and signed by the board
- Appoint a compliance officer to ensure compliance
- Train the employees in AML compliance
- Have an independent review done by a third party
- Do customer due diligence to assess the risk of doing business with them
AML Solutions and Best Practices
In general, fintech and FIs are expected to take the following steps to ensure compliance with the anti-money laundering act:
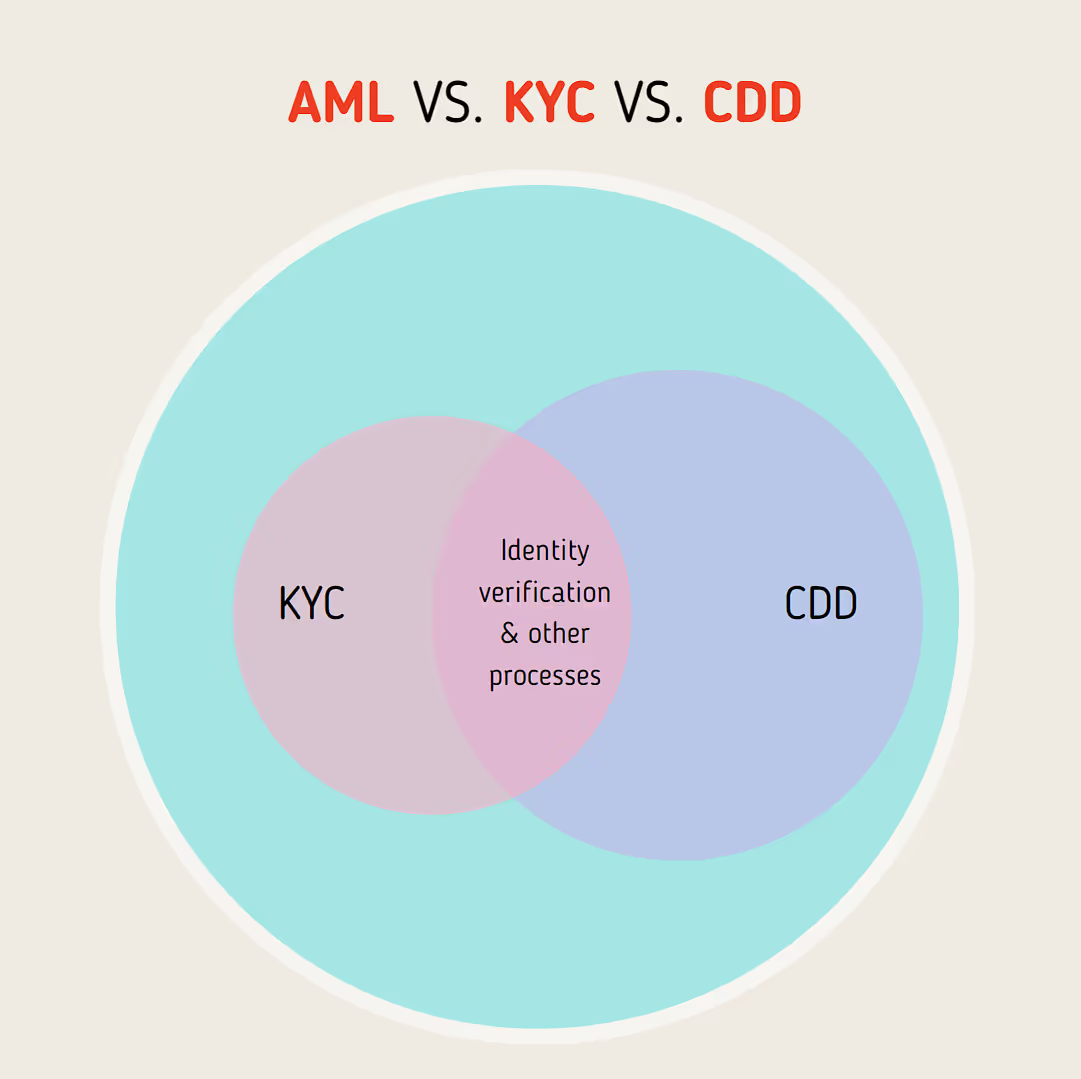
Know Your Customer (KYC)
It’s the process of verifying the identity of a client:
- Collect and verify documents such as Passport, proof of address
- Regularly update the KYC information
- Categorise customers based on risk and apply enhanced due diligence (EDD) for high-risk customers
The goal is to ensure customers are who they claim to be and to assess potential risks of illegal intentions. It also allows FIs to trace each transaction to an organization.
Customer Due diligence (CDD)
CDD is a more comprehensive process that includes KYC but goes beyond it. It involves assessing the risk profile of the customers based on their background, financial status, and the nature of their transactions:
- Verify the identity of customers
- Identify and verify the beneficial owners of legal entity customers
- Understand the nature and purpose of customer relationships to develop a risk profile
It also includes ongoing monitoring of customer transactions to detect and report suspicious activities. If any unusual patterns or high-risk indicators are identified during this process, it may trigger the need for EDD. It involves more rigorous checks like:
- Obtaining additional information about the customer and business
- More frequent updates of customer information
- Closer scrutiny of the customer’s transactions
- Obtaining senior management approval to establish or continue the business relationship
Proper Reporting and Transaction monitoring
To the FIU, FIs must report suspicious transactions—Suspicious Activity Reports (SARs) and Currency Transaction Reports (CTRs).
Transaction monitoring systems detect unusual or suspicious transactions. They analyze transactions in real-time or batch mode to identify patterns that may indicate laundering. Compliance officers review the alerts generated by these systems. Report transactions above Rs 1 million to the FIU.
Wallet Screening
For cryptocurrency FIs, wallet screening involves verifying the source and destination of crypto transitions to ensure they aren’t linked to illicit activities. Wallets are screened against known blacklist wallets to identify high-risk transactions.
Use Case: Data-Driven Decision Making in AML
Data-driven decision-making can help FIs bolster their AML capabilities. By leveraging advanced analytics and comprehensive data aggregation capabilities using services like Neokred’s ProfileX, you can transform your AML efforts. Here’s how:
- Data aggregation: ProfileX aggregates transactional and non-transaction data from multiple sources, giving you a holistic view of customer behavior to help detect patterns indicative of money laundering.
- Risk-based assessments: Using advanced analytics, ProfileX can conduct risk assessments based on alternative data, such as behavioral insights. This enhances the accuracy of identifying high-risk customers.
- Real-time monitoring: ProfileX monitors customers’ transactions in real-time, allowing you to identify and respond to suspicious activities promptly.
Anti-Money Laundering and Neokred
AML compliance protects FIs and fintechs from reputational damages and regulatory penalties while fostering a secure financial system. However, while AML measures are necessary, traditional KYC processes can be cumbersome, leading to a poor user experience.
Neokred’s ProfileX addresses this challenge head-on, offering a streamlined approach to onboarding, KYC, and CDD using a name and mobile number. Then, it captures quality information from the documents and aggregates it in real-time to complete user profiles. It also offers insights into customers’ behavior, preferences, and creditworthiness to help detect potential fraud early on. API integration also minimizes disruption to existing operations.
Moreover, ProfileX is designed with regulatory compliance at its core, adhering to banking and data protection regulations. To explore how Neokred can improve your AML compliance and streamline customer onboarding, contact us here.
Conclusion
FAQs
Here are some key elements to keep in mind while choosing an AML software:
- Assess your needs; focus on size, type, risk profile, and regulatory requirements
- Define critical features like CDD, translation monitoring, and suspicious activity reporting
- Ensure the software is scalable and adapts to changing regulations
- Ensure it seamlessly integrates with your existing systems
The critical requirements for training employees in AML compliance are:
- Awareness of the company’s AML policies and the government’s AML regulations
- Role-specific training
- Training employees on CDD and transaction monitoring
- Ensure employees understand the importance of maintaining accurate records
- Training employees on the company’s AML software
AML policies should evolve with your business and regulatory landscape; some common cases include the following:
- A minimum of one comprehensive annual review is required
- Update policies when new laws or regulations are introduced
- Review policies when a business undergoes significant changes
- Update policies based on risk assessment results





